VPN services provide us with security and privacy online. But the Internet is a complicated place, with many services and technologies working together to give us the seamless access we expect. As a result, there are many ways mistakes can occur, ways our security or privacy can be compromised.
One such way is through what is known as a DNS Leak and if you are not careful in choosing a VPN that protects against this, then your DNS could indeed leak. In this article we are going to get into the weeds a bit and explain in detail what you need to know about DNS leaks.

. In this article we will discuss:
- What a DNS Leak Is and Why You Should Care
- How to Find Out if You Have a DNS Leak
- Common Causes of DNS Leaks and Their Solutions
As you are about to see, there are several ways such a leak can happen, but also steps you can take to prevent them, or fix them if they do occur.
Let’s get started.
What a DNS Leak Is and Why You Should Care
To understand DNS Leaks, you need to know what DNS is and how it works. If you already know about this, feel free to skip ahead. If not, here is your 2-minute lesson in a portion of the Internet most people don’t even know exists.
What is DNS?
DNS stands for Domain Name System. It is the crucial link between human-readable names for websites and the names that computers use for those sites. Websites are identified by their IP Address.
Most IP Addresses look something like this when written out: 72.21.215.90
The four numbers each range from 0 to 255. Collectively they identify an individual connection to the Internet, such as an individual device, a network, or your favorite website.
The above represents the older IP Address system, known as IPv4. As the world is running out of available IPv4 addresses, the Internet is slowly transitioning to a newer system, IPv6. In IPv6, an address looks something like this when written out: FE70:CE00:0000:0CDD:1238:0000:211F:618B

Imagine if to reach your favorite websites you had to enter addresses like these instead of ones like Blokt.com, or Gab.ai? It would cripple the entire Internet. This is why they invented DNS. DNS translates the human-readable names we use into the computer readable addresses that look like those monsters above.
So what is a DNS Leak?
A DNS Leak occurs when your requests to a DNS server are visible to outsiders.
Using a DNS service is dangerous because it gives away a lot of information about your online activities. If you are not protected, anyone watching the DNS server (not to mention the people who run the service) will be able to see the names and IP Addresses of every website you visit. While this doesn’t tell anyone what you did while you were connected to the website, this information can still be very valuable to outsiders, and something you don’t want to share.

The fact that you frequently visit websites about an incurable disease could be very valuable to your insurance company. The fact that you are reading up on prenatal care could be quite a shock to your parents or your husband who is stationed overseas. And the fact that you are a regular in certain online discussion areas could be literally life-threatening if you live in certain repressive countries.
In a perfect world, your VPN service should protect not just your Internet communications but your DNS activities as well. But since this isn’t a perfect world, we have DNS Leaks. If you are downloading torrents or doing something private then you never want this to happen.
Now that you know what these are, and how much of a problem they can be, let’s check your device and see if your VPN is leaking DNS information at this very moment.
How to Find Out if You Have a DNS Leak
There are several websites that claim to help you see if you have a DNS Leak. The one we like to use is called IPleak.net. It is fast and easy to use. The site is capable of looking for IPv4 and IPv6 leaks, as well as several other related problems.

To show you how this site works, we will walk you through the process of running its tests using one of the computers in our lab. The test machine is a Linux desktop running ExpressVPN, but the steps are the same for any computer and any VPN.
Using IPleak.net
Using IPleak.net is about as easy as it gets. Follow these steps:
- If it is not already active, turn on your VPN. It will be helpful to know where the VPN server you are using is located.
- Browse to https://ipleak.net/.
- Review the results that appear. You should see something like the following image:
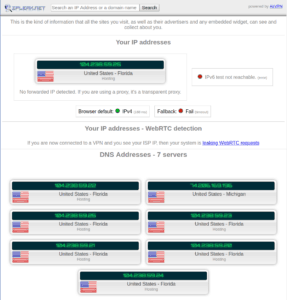
Analyzing the results is pretty simple too. Look at every box that appears on the screen with an IP Address in it. None of the IP Addresses you see should be related to your actual address. If they are, you have a leak.
In this example, most of the addresses are in Florida, which is the location of the VPN server I am using. For whatever reason, one of the addresses is in Michigan.
That’s a surprise, but I know it is nothing to worry about since my actual location is not anywhere in North America.
If you are ever unsure whether an IP Address you see is a problem, try turning off your VPN then reload this page to see if the addresses match.
How Often Should You Test for Leaks
If your testing doesn’t show a DNS Leak, you are in good shape. For the moment. But the fact that you don’t have a leak today isn’t a 100% guarantee that you won’t have one tomorrow. So how often should you test your devices for leaks?

We don’t have a one-size-fits-all answer to this. It makes sense to us to redo these tests whenever you update your operating system, web browser, or VPN. Also whenever you are about to do something that you would like to keep private.
Common Causes of DNS Leaks and Their Solutions
Now that we have all the preliminaries out of the way, let’s look at the common causes of DNS Leaks and how you can plug them. The problems we will be talking about are:
- Incorrect Network DNS Settings
- IPv6 Transition Problems
- Transparent DNS Proxy Redirects
- Smart Multi-Homed Name Resolution
Incorrect Network DNS Settings
Whenever you connect your device to an ISP or network, the device must look for connections to DNS servers and the Internet in general. Whether this is a problem or not will depend on the VPN you use.
Your VPN Doesn’t Provide its Own DNS
Devices are typically configured to ask the local network or the ISP what DNS service to use. It will connect to that service through an unencrypted connection, and whoever provides the service will log whatever information they can about your activities. This is clearly not good.

You have two options here. The first is to change the network settings on your device to tell it to always use the third-party DNS that you specify. You can usually configure the operating system on your device to point to a service like DNSWatch or Verisign DNS that provides better privacy protections than your ISP is likely to.
The details on how this is done vary from operating system to operating system.
Your second option is to switch to a VPN service like ExpressVPN or NordVPN that provides its own encrypted DNS service.
Your VPN Provides its Own DNS Service
If your VPN provides its own DNS servers, you should be fine. In most cases, the VPN will encrypt DNS requests and send them through its encrypted tunnel to its private DNS servers. That eliminates the possibility of anyone on the local network or at your ISP of seeing that information.

One Last Thing to Check-in Either Case…
That said, it always pays to confirm stuff like this. Some ISPs are resorting to a technology called a Transparent DNS Proxy to in effect hijack your DNS requests and force them through the ISP’s DNS. In the next section, we’ll show you how to spot this obnoxious trick and get around it.
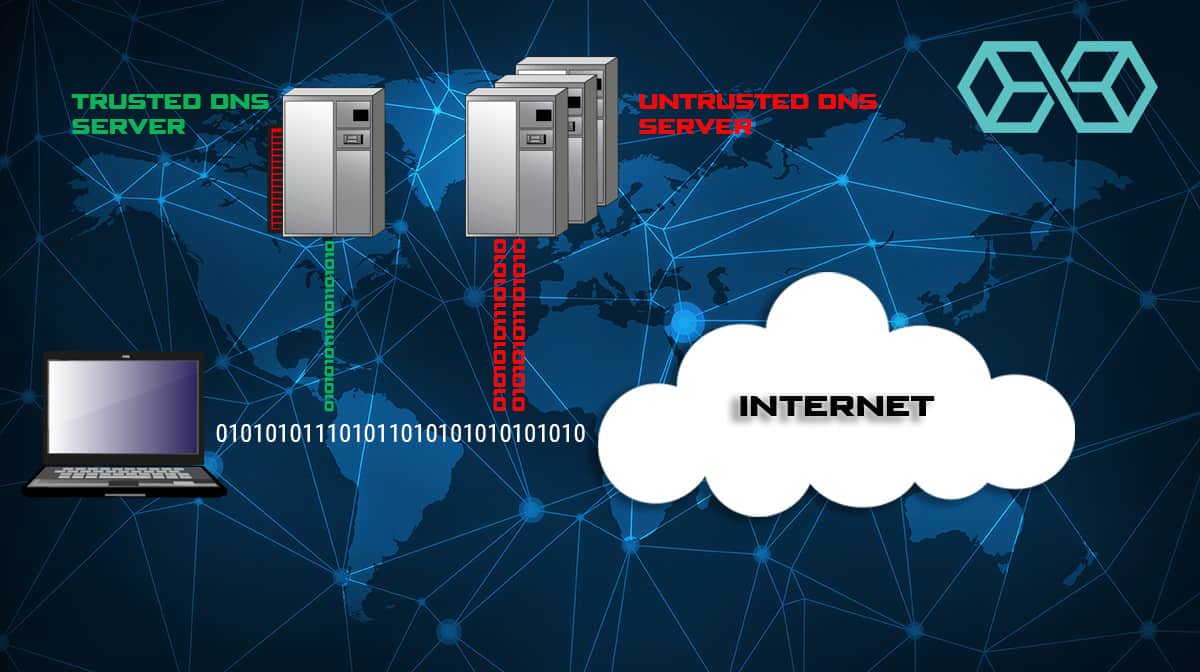
Transparent DNS Proxy Redirects
If you don’t like the idea of using whatever DNS is provided by the ISP you are using at the moment, and your VPN doesn’t provide its own, you have options. You can usually change the settings in your devices to tell them to use a particular DNS service, rather than the one the ISP wants you to use.
Services like DNSWatch provide a privacy-oriented DNS without logging your activity or censoring what sites you can visit. ISPs don’t like this.
The Problem
To keep you from using the DNS of your choice, some ISPs use Transparent DNS Proxy redirects to force you to use their DNS servers. This benefits them because they can gather information about what sites you visit. Information about what users do online is very valuable, particularly in the United States, where ISPs can legally sell information about your online activities to anyone waving enough cash.
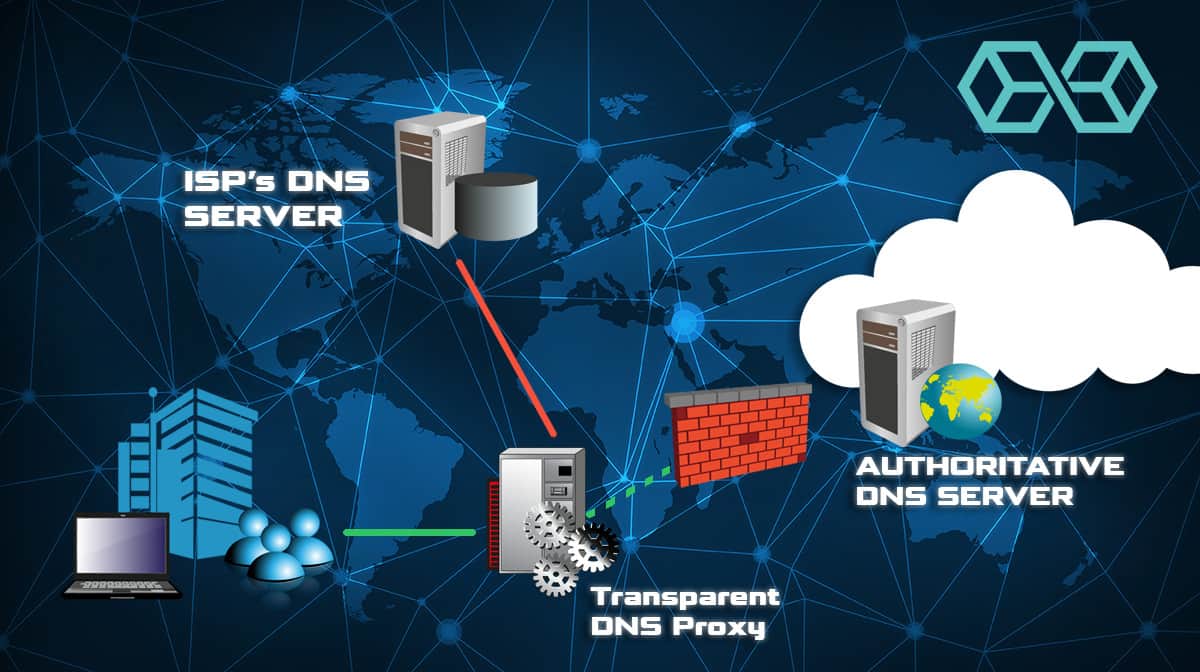
The Transparent DNS Proxy watches for any DNS requests going to TCP/UDP Port 53 and without your knowledge (transparently) redirects them to the ISP’s own DNS servers. It is pretty sneaky. They are basically imposing a DNS Leak on you so they can capture your information.
How to Tell if Your ISP is Redirecting DNS

There is no easy way to tell if your DNS requests are being redirected. One way to get a good indication is to ping a non-existent domain (techforyou2.com is one such non-existent domain).
If your DNS is not being redirected, you should see an error message that looks something like this: “ping: unknown host techforyou2.com”.
If you don’t get an error message, your DNS requests are probably getting redirected by a Transparent DNS Proxy. To try this for yourself, visit this wikiHow page. It has instructions on how to ping using various operating systems.
The Solution
There are a couple of ways to attack this problem. One is simply to choose a VPN service that provides its own encrypted DNS servers. By encrypting your DNS lookups and keeping them inside the VPN tunnel, a VPN makes it impossible for a transparent DNS proxy to see them to redirect them.

If your VPN uses the OpenVPN client you can set the block-outside-dns option in the OpenVPN configuration file. See this page for instructions.
IPv6 Transition Problems
As we mentioned earlier, the Internet world is making a slow transition from IPv4 to IPv6. It has been underway for years, and will probably take many more years to be completed if it ever is.
The effort required to convert everything connected to the Internet to use IPv6 is enormous and extremely costly. The upgrade will be great for the makers of Internet of Things (IoT) devices and will make it easier to keep adding users to the Internet, but there aren’t any visible benefits to the consumers who will have to pay for all the work.
The Problem
Most VPN services don’t support IPv6. They can’t justify it economically and there is no pressure from their customers to make the investment.
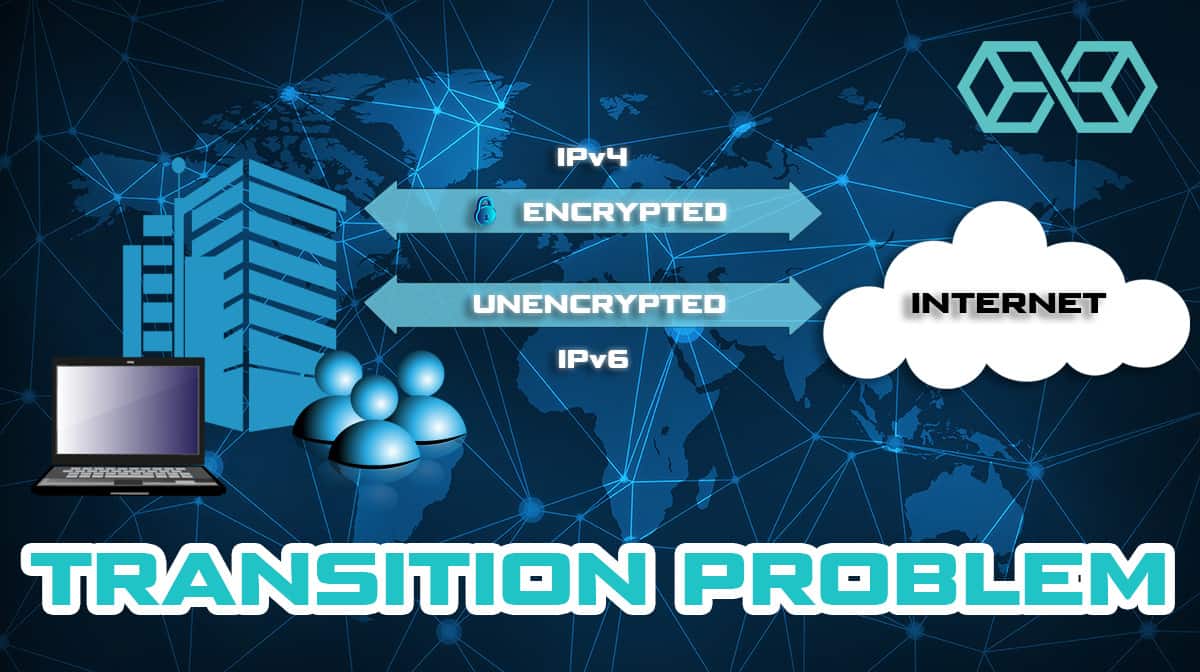
But many websites and Internet services support both IPv4 and IPv6. Rumor has it that there are even some locations on the Internet that only use IPv6. So the question is what does your VPN do if it needs to connect to a site with an IPv6 address?
The Solution
Some VPNs simply send the DNS requests outside the tunnel to the ISP’s DNS or whatever DNS is available that does support IPv6. IPVanish is one of the VPNs that take this approach. While this does solve the problem of getting the DNS information you need, it is also a DNS Leak.

Other VPN services will simply block any IPv6 requests. This is the approach both NordVPN and ExpressVPN use, along with many of the other best VPN services. It prevents a DNS Leak at the cost of possibly leaving you unable to get DNS information for certain sites.
The ultimate solution to this problem would be to use a VPN that provides full IPv6 support and its own DNS servers.
Microsoft Teredo
Here’s another problem caused by the slow transition from IPv4 to IPv6. Microsoft’s Teredo technology is designed to allow the use of IPv6 addressing when it is not otherwise supported. The technology works by encapsulating IPv6 traffic inside IPv4 packets. These packets carry the IPv6 traffic back and forth between your device and Teredo Relays, nodes that connect to IPv6 services.
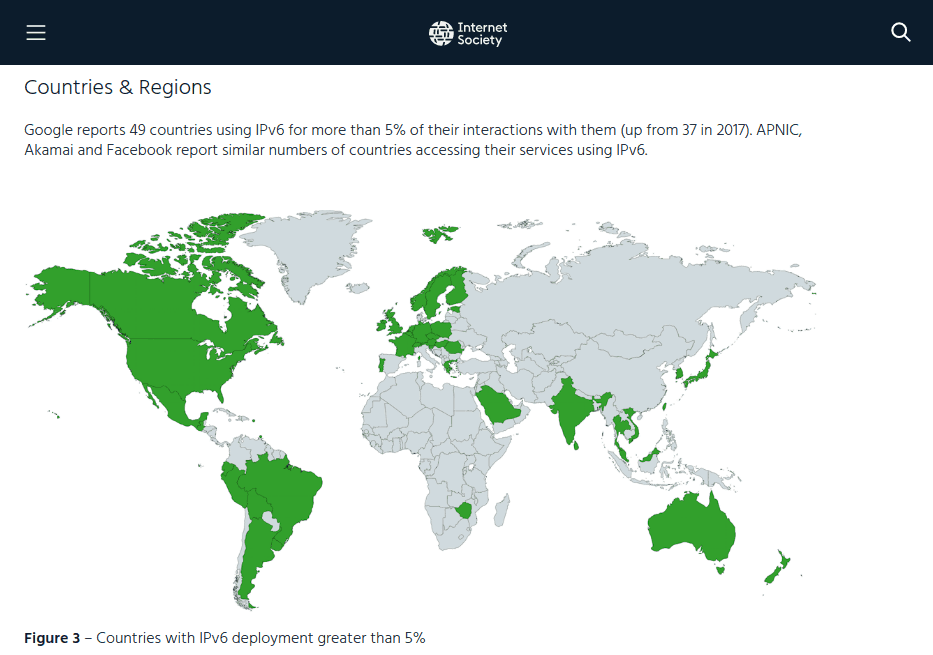
Teredo is meant to be a temporary fix for the lack of universal IPv6 support. Given the rate of progress with the IPv4 -> IPv6 transition Teredo is likely to be around for a long time. According to this 2018 Internet Society report, 49 countries in the world have more than 5% of their Internet traffic on IPv6. As the following screen capture shows, there is a long way to go.
The Problem
Teredo is built into recent versions of Microsoft Windows. Like your VPN service, Teredo is a tunneling technology, which opens up the possibility of conflicts. Rumor has it that the Teredo tunnel can supersede your VPN’s tunnel, effectively stripping away the privacy and security your VPN provides. While we haven’t experienced this problem, we agree that Teredo can cause problems.
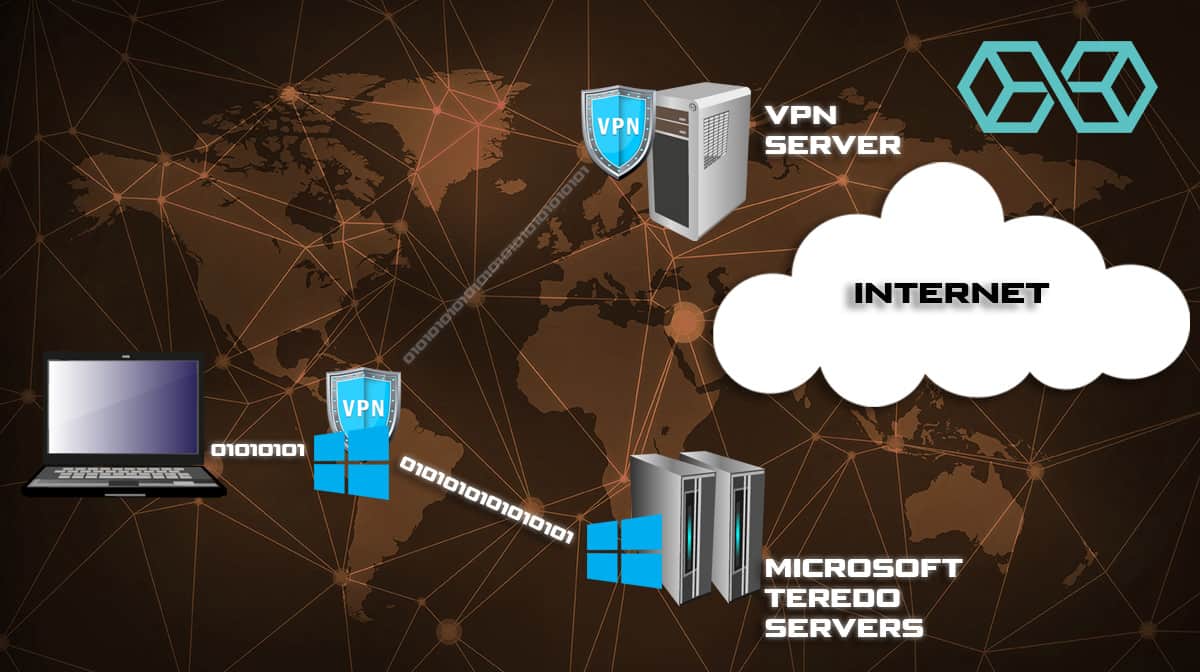
If your VPN doesn’t support IPv6 and doesn’t block IPv6 traffic, any IPv6 DNS requests your device makes will likely get pulled into the Teredo system. As would any messages between your device and the IPv6 site you are talking to. That would leave everything you do exposed to whoever runs the Teredo Relays.
The Solution
The solution is simple. Turn off Teredo!
Smart Multi-Homed Name Resolution
Smart Multi-Homed Name Resolution is a technology Microsoft added to Windows, starting with Windows 8. The idea is to improve Internet performance by sending out DNS requests to any available DNS servers instead of just the one you select.
The Problem
The problem with this is that blasting your DNS requests all over the place turns every query into a DNS Leak. This “feature” tries to send DNS requests to your ISP’s DNS and any other DNS servers it can see, even if your VPN service is securely sending the queries through the VPN tunnel to safe DNS servers. This introduces all sorts of security issues, even prompting US-CERT, a division of the Department of Homeland Security to publish a bulletin about the risks.
This was a headache in Windows 8, but at least you could turn it off. It became a bigger headache in Windows 10. In Windows 8 your DNS requests were sent to every DNS server the system could see, but it only used the alternate services if the primary one failed to respond. In Windows 10, the system uses the first response it receives. That means you have no control over which DNS service you use.
Adding to the fun, Microsoft took away the ability to turn off Smart Multi-Homed Name Resolution in Windows 10 Home Edition. The millions of users with that version of Windows are stuck with this major security problem.
The Solution
Unfortunately, there are only partial solutions to this problem. The first thing to do is to install a VPN with DNS Leak Protection (NordVPN for example) if you don’t already have one. Turning on this VPN feature will usually disable Smart Multi-Homed Name Resolution in Windows 8 and may work for Windows 10 as well.

If you aren’t afraid of changing Windows Registry settings there are instructions available online that will disable Smart Multi-Homed Name Resolution for Windows 8 and Windows 10. Note that these instructions won’t work for Windows 10 Home users. Instead, there is a partial workaround. You can find the instructions here.
Conclusion
DNS Leaks are a relatively unknown risk for VPN users. While the best VPNs take steps to ensure that your DNS requests don’t leak out to people who will exploit that information, even they are not immune to the problem.
As this article shows, you can easily find and fix (or at least mitigate) most of these problems if you don’t mind making some changes in the operating systems of your devices. Users of Microsoft Windows 10 will have the most problems, thanks to some Microsoft changes that are supposed to improve your browsing experience but inadvertently introduce leaks.
If you would rather not mess around in the guts of your equipment, the easiest way to deal with most of these problems is to switch to a VPN like Nordvpn, Surfshark, Expressvpn or one of our other best rated VPN’s. By providing their own encrypted DNS servers and making it easy to block IPv6 communications these two industry leaders take care of most of these issues for you.
![A Beginner’s Guide to Monero – What Is XMR? [Updated 2023]](https://cd.blokt.com/wp-content/uploads/2019/04/Beginners-guide-to-Monero-2-218x150.png)

![Best 5 Bitcoin Sports Betting Sites [2023] (Analyzed & Approved) Best Bitcoin Betting Sites](https://cd.blokt.com/wp-content/uploads/2020/05/best-bitcoin-betting-sites-218x150.png)

